MS SQL Pentest
In few of me internal pentest engagement I was able to enumerate IP and credentials of database server, either by brute-forcing or searching the code for database connect string.
In last 6months I got the database credentials twice in client side code excluding the successful brute-force.
Previously when I use to get the credentials, I try to connect the server using a local client. Eg. If I get credentials of MS SQL Server then I download some client for it and try to view the database.
This time I was not really interested in doing that. Instead I was thinking to escalate my privilege and do something more than just viewing the database, because when I was reading the walk-through of Kioptrix it states that we can gain code execution using some commands executing in sql format.
So I googled ways to enumerate mssql and I got a very good link https://www.offensive-security.com/metasploit-unleashed/admin-mssql-auxiliary-modules/
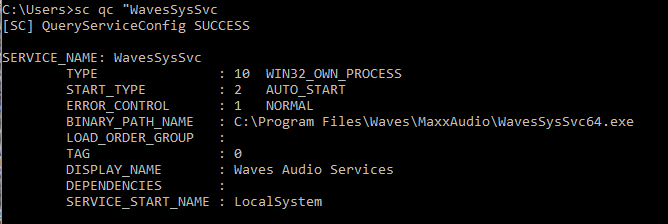
So starting with enumeration I used mssql_enum auxiliary module for enumeration:
Running the module enumerated many descriptive information.
xp_cmdshell is Enabled so we can try to execute commands on the server.
The “mssql_exec” admin module takes advantage of the xp_cmdshell stored procedure to execute commands on the remote system. If you have acquired or guessed MSSQL admin credentials, this can be a very useful module. (Ref: offensive security)
Configuring mssql_exec metasploit module as shown below.
The "set CMD ipconfig" command will set the command to be executed on the remote host.
Then just run it.
Checking out whoami.
Then I tried of gaining a meterpreter session on the server by referring https://www.offensive-security.com/metasploit-unleashed/payloads-mssql/
Tried many permutation combination and other payload, nothing really worked so far.
Tried uploading wget vbscript on the server but it failed as the module mssql_exec doesn't support special character in its set CMD syntax.
*******************************
Revalidation of the finding
The developer team said that they have fixed the finding and send us the application for revalidation.After traversing the previous path I saw the following:
Basically they were calling a "....Script.vbs" script from a javascript.
Then I entered that .vbs file name in the URL :
File download was shown to me.
After downloading and reading the file I got the connect string again.
Reported the finding.
Now the developers has stored the connect string in web.config file, still it can be accessed.
Ref: http://hugoware.net/blog/dude-for-real-encrypt-your-web-config









Prepare4Test the best and reliable platform where you can get accurate ASF question dumps which will assist you in passing your EXIN Agile Scrum Foundation exam fast.
ReplyDelete