De-Ice 1.20b Walkthrough
Well 15 days back I have written Walk-through of De-Ice 1.120a On My Blog. I got great response by vulnhub and they published my walk-through https://www.vulnhub.com/author/trnform3r,152/
With a such a warm encouragement I feel like writing more walk-through.
Here Is my walk-through on De-Ice 1.20b. You can download the VM and get more info about it form here.
Note: The attacker machine and the VM should be in the subnet of 192.168.1.0/24
Labsetup:
1 - Open Vmware - > Edit - >"Virtual Network Editor"2 - Click on "Add Network" and add any 1 Network example VMnet2
3 - Select VMnet2 and change Subnet IP - 192.168.1.0 and Subnet mask -
255.255.255.0 also select "Host - Only"
4 - Now add this adapter VMnet2 for both the machine.
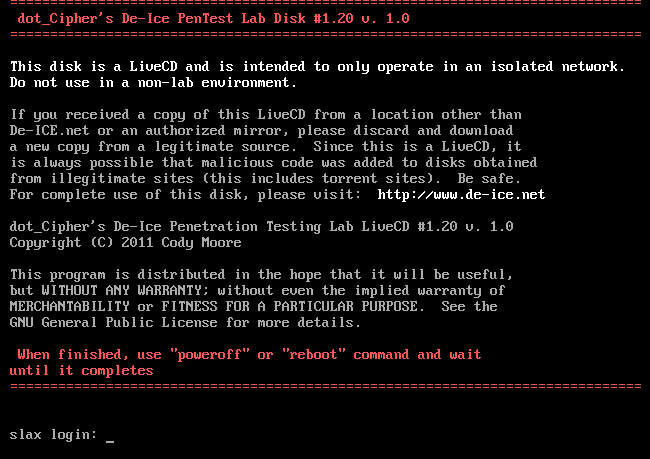
When you start the VM it looks something like this.
Ohk so when we talk about De-Ice series the one thing that they want us to know, learn and practice is making up the dictionary and brute-forcing.
Lets startup with the VM.
Enumeration:
Enumeration begins with nmap.
Anonymous login was enable but the FTP link was broken. So port ftp/21 is of no use. Moving on some generic ports such as 22, 25 and 80 were open.
Next step was to run a Nikto scan on the website.
It seems to be "The BANK of no Security Company Portal" with an customer service email disclosed on the page.
No the signature of De-Ice series is that they give you some names,email id or information about staff etc. You have to make list of username and password in-order to brute-force the accounts.
So then I made few combination of names from the email id and other information that were given on the page, stored it in username file and started brute-forcing for SSH.
No the signature of De-Ice series is that they give you some names,email id or information about staff etc. You have to make list of username and password in-order to brute-force the accounts.
So then I made few combination of names from the email id and other information that were given on the page, stored it in username file and started brute-forcing for SSH.
I was watching one of the video on securitytube.com where Vivek Ramachandran uses and encouraged to use ncrack commenting that it is more stable to use. So I used ncrack this time just for a change. And I got a username and password as shown below.
Now ssh login using csadmin
csadmin account contains a directory i.e mailserv_download that contains 2 files.
CAT the file gave me a mail conversation.
Then I checked /etc/passwd file to check all the users.
Then I added all these usernames and few words from the mail conversation to make a dictionary to get the root login.
After some permutation combination and referring g0tmilk, I brute-forced and got sdadmin credentials using ncrack. I was expecting other way round but still it was all about bruteforce this time.
Now login in using sdadmin gave me the same mail server folder that I got from csadmin account.
Reading the mail conversation from sdadmin account is as follows.
Again the same bruteforce loop. This time it took long for me to get proper credentials as I was not trying out any more combination to my previous dictionary.
But then suddenly I got a username password combination as follows.
SSH using the new credentials received.
This time when I try to cat the file. It was quite obfuscated and unreadable. So I tried to stings the file and I got a java program.
The subject clearly mentions "New Custom Encryption for Passwords" .
There are three found parts so far, which has been written in java and the function of it was the generation function for the new passwords policy. There are comments left in the code, saying it has already been used on two accounts (sysadmin and root).
I am not that good at java so I referred g0tmilk code it had some error so I fixed, compiled and executed the code to get priviledge escalation done to sysadmin and then finally to root.
Game over.......
Thanks to g0tmilk for the java code deice.java
import java.io.*;
//import java.util.Arrays;
public class deice
{
import java.io.*;
//import java.util.Arrays;
public class deice
{
public static void main(String[] args)
{
try
{
System.out.println("[>] De-ICE.net v1.2b (1.20b) Password Generator");
BufferedReader in=new BufferedReader(new InputStreamReader(System.in));
System.out.print("[?] Username: ");
String input=in.readLine();
int[] output=processLoop(input);
//System.out.println("[+] Output: "+Arrays.toString(output));
String outputASCII="";
for(int i=0;i<output.length;i++) outputASCII+=(char) output[i];
System.out.println("[>] Password: "+outputASCII);
}
catch(IOException e)
{
System.out.println("[-] IO Error!");
}
}
/*input is username of account*/
public static int[] processLoop(String input){
int strL=input.length();
int lChar=(int)input.charAt(strL-1);
int fChar=(int)input.charAt(0);
int[] encArr=new int[strL+2];
encArr[0]=(int)lChar;
for(int i=1;i<strL+1;i++) encArr[i]=(int)input.charAt(i-1);
encArr[encArr.length-1]=(int)fChar;
encArr=backLoop(encArr);
encArr=loopBack(encArr);
encArr=loopProcess(encArr);
int j=encArr.length-1;
for(int i=0;i<encArr.length;i++){
if(i==j) break;
int t=encArr[i];
encArr[i]=encArr[j];
encArr[j]=t;
j--;
}
return encArr;
}
/*Note the pseudocode will be implemented with the
root account and my account, we still need to implement it with the csadmin, sdadmin,
and dbadmin accounts though*/
public static int[] backLoop(int[] input){
int ref=input.length;
int a=input[1];
int b=input[ref-1];
int ch=(a+b)/2;
for(int i=0;i<ref;i++){
if(i%2==0) input[i]=(input[i]%ch)+(ref+i);
else input[i]=(input[i]+ref+i);
}
return input;
}
public static int[] loopBack(int[] input){
int ref=input.length/2;
int[] encNew=new int[input.length+ref];
int ch=0;
for(int i=(ref/2);i<input.length;i++){
encNew[i]=input[ch];
ch++;
}
for(int i=0;i<encNew.length;i++){
if(encNew[i]<=33) encNew[i]=33+(++ref*2);
else if(encNew[i]>=126) encNew[i]=126-(--ref*2);
else{
if(i%2==0) encNew[i]-=(i%3);
else encNew[i]+=(i%2);
}
}
return encNew;
}
public static int[] loopProcess(int[] input){
for(int i=0;i<input.length;i++){
if(input[i]==40||input[i]==41) input[i]+=input.length;
else if(input[i]==45) input[i]+=20+i;
}
return input;
}
} 
















Comments
Post a Comment